Introduction
In recent years, e-services have gradually and significantly expanded from the perspective of buying and selling of a service or product. Despite the early failure of its popularity due to high equipment cost necessary for the operations and high connection fees, the World Wide Web (www) has paved the way to enable the developers in the area of banking applications to take advantage of the Internet as a means to support and spread their service.
E-banking creates unprecedented opportunities for the banks in the manner they organise financial product development, delivery, and marketing via the Internet. The speed and scale of these challenges have rapidly increased with the pervasiveness of the Internet and the extension of information economy (Holland and Westwood, 2001).
The use of e-banking technologies such as Automated Teller Machines (ATMs), Tele-banking, home banking and internet banking in the delivery of banking products and services has increasingly become an essential aspect of contemporary banking systems (Mols, 1998).
The use of technology in various segments of society around the world has given the opportunity to all service providers to offer a bouquet of services in the e-banking framework. Wei and Howell (2010) classified e-banking services from the e-business perspective: Business to Business (B2B), Business to Government (B2G), Customer to Business (C2B), and Business to Customer (B2C).
This expansion and diversification requires provision of service 24/7 with very low failure rates to customers. This indeed shows the progress and expansion of e-banking services.
While e-banking has offered new opportunities, it also poses many challenges such as the innovation of IT applications, the blurring of market boundaries, the breaching of industrial barriers, the entrance of new competitors, and the emergence of new business models (Saatcioglu et al., 2001; Liao and Cheung, 2003).
Banks must constantly reconfigure, renew, or gain organisational capabilities and resources to meet the demands of the dynamic environment (Wu et al., 2006).
A review of literature showed that only been a few studies are available about ICT adoption in developing countries compared to the developed countries. Therefore, this paper aimed to bridge this gap by identifying and exploring the key components that enable e-banking in an integrated picture to the banks customers; this may also help in avoiding wastage of investment and efforts of decision-makers and developers when seeking to develop e-banking services.
It also aimed to determine the technical resources and IT capabilities that must be taken into consideration for raising the level of e-banking in commercial banks. The key strategic decisions of a bank in developing e-banking capabilities and factors that influenced these decisions and the lessons that can be drawn from this case were explored as a whole.
The use of case study approach facilitated the evaluation of these issues of e-banking within the real-life context.
This research attempted to address how IT capabilities enabled e-banking. This project studied previous literature, which discussed IT capabilities and its relationship to performance within firms. This review has compiled all the factors and combined them according to the conclusions that resulted from these previous studies so as to clarify the relationship of IT capabilities in enabling e-banking services.
Literature Review
During the period 2000—2011, a number of studies, as discussed below, were conducted on the impact and role of IT capabilities in e-businesses, particularly, the banking sector. These studies focused on examples from both developed and developing countries, as well as on all the electronic banking (e-banking) divisions. Most of them presented the concept of adoption or acceptance of e-banking from the perspectives of both consumers and service providers.
Moreover, other researchers have shown a framework for assessing e-banks (Al Saud and Abdallah, 2004). The objective of this research was an attempt to analyse previous research studies that dealt mainly with IT capabilities enabled e-banking in developed countries, and in developing countries in particular.
Yoon (2011) defined IT capabilities as the ability to integrate with other resources within the organisation through the use and employment of IT resources. This definition conformed to Bharadwaj et al. (1999) and Jiao et al. (2008).
Furthermore, Yoon (2011) and Bharadwaj et al. (1999) formulated this definition more precisely by stating ITC to be the ability to organise in support of organised activities and workflow through the disposition of IT resources and integration of other relevant resources.
Here, Lee et al. (1995) particularly agreed that ITC is a kind of organisational ability to unite relevant resources.
De Jong et al. (2009) used “IT resources” as a generic term encompassing the IT infrastructure, people, capital cost, and all other elements that lead to the delivery of IT services. Moreover, it was assumed that both IT resources and IT capabilities are part of IT assets that should aim to deliver the potential services.
However, most studies that dealt with ways of measuring IT capabilities examined these capabilities on several levels and influencing factors.
Table 1 lists the factors required to measure IT capabilities. Moreover, Araya et al. (2007) attempted to address these capabilities into three levels: technical capabilities, managerial capabilities, and organisational capabilities.
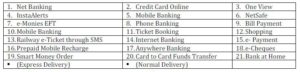
Table 1: Factors Used To Measure IT Capabilities

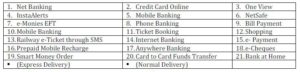
Rahman’s (2007) study attempted to explore the role of IT within the banking sector. His study focused on the role of IT from a single perspective, which was the investment of banks in developing an IT infrastructure. He listed out the technology products offered by the banking sector (Table 2).
Table 2: IT Infrastructure Products in the Banking Sector
According to Okunoye et al. (2007), these products are innovations in the banking sector as well as in the development that occurs in e-services and the design of e-banking to align with IT. Online banking, mobile banking, point of sale (POS), and ATM fall within the framework of innovations in the banking sector. As such, Okunoye et al. (2007) suggested that more research should be done in this field in future, especially in developing countries.
There is lack of sufficient studies on this aspect of banking. Their study confirmed that IT has a major impact on all stages of banking applications and that banks should invest in IT infrastructure to give them significant help in providing a variety of channels to deliver banking services to their customers. The adoption of innovations in IT and the factors that contributed to the delay in the adoption of these innovations among the e-services sectors in developing countries were highlighted.
This present study has discussed these points by exploring a case study of a Nigerian bank. The study researched a number of questions regarding the causative factors in adopting new IT to provide e-services; they included applying the latest technology to information, the factors that cause the adoption of new technology, and the main obstacles that hinder the adoption of IT.
Although the researchers discussed these issues in order to understand how to apply new technologies within financial e-service institutions, the study itself did not focus directly on IT capabilities or on its impact on e-services.
Okunoye et al.’s (2007) study listed the IT capabilities in a number of small and medium enterprises (SMEs), but does not provide detailed information that would explain the differences between these institutions in their reliance on IT.
Electronic banking services, encountered as one of the common delivery channels of commercial banks, have enabled most businesses to complete payment processing and transfer funds electronically. A number of researchers have concluded that the adoption of Internet technology in the banking sector is the chief factor in the spread of e-banking.
Floh and Treiblmaier (2006) asserted that online banking, which provides different banking services, is a key player in attracting customers. This point may explain the existence of the common connection between e-banking and IT capabilities that is held by commercial banks.
On the other hand, other researchers like Almazari et al. (2008) were of the view that attracting new customers or keeping the loyalty of the current customers cannot be accomplished adequately through websites of bank services.
Since this method offers little or even no focus on customer relationship management (CRM) by the banks, it may result in loss of customers, who will move on to other competitors who do a better job of managing customer relationships.
A number of banks operating in developing countries have adopted e-services as one of the emerging technologies where the various e-services were affected by culture, environment, or the adoption by customers and services providers themselves (Ben-Jadeed 2004).
However, knowledge in e-banking remains the real challenge to the growth of e-banking in developing countries (Salehi 2010). Auta (2010) claimed that e-banking in developing economies faced other challenges such as security, user-friendliness, queue management, accessibility, time factors, and funds transfer.
Researchers have tried to discuss the factors affecting e-banking services from several aspects of the pool. The majority of studies show that the element of security and knowledge are major players affecting the success of these services in developing countries.
Al-Hajri (2008) noted in his study on the adoption of e-banking by the Omani banks that security and knowledge are not the only factors, but the communications infrastructure also affects the adoption of it. This clearly refers to the ITC in enabling e-banking and raising the quality of e-banking services.
Berger (2003) pointed out that Internet banking, electronic payment, and information exchange are not the most important technological products in the banking sector, but illustrated the potential differences and measured technological progress in the front office.
Most of these studies focused on the role of IT capabilities in the firms and their relationship with the performance only. International standards frameworks such as Control Objectives for Information and Related Technology (COBIT), Information Technology Infrastructure Library (ITIL), or Capability Maturity Model (CMM), etc. aimed to provide solutions to measure IT capabilities and the way of business processing in any commercial enterprise to determine their level of performance.
Davenport (2005) classified these standards based on three main areas: the first group of standard focused on the process activities and flows, the second group of standards focused on press performance and the last set of standards focused on the process management.
He confirmed that these international standards alone are not sufficient to achieve the goals of the company. Each firm has a business theme, which is unique and truly impacts the performance of work; and this really complicates the issue for the developers or decision-makers within commercial banks to create a specific mechanism to determine the capacity of IT that enables e-banking on a higher level in line with the ambition of customers.
Such international standards only help in facilitating the operations outsourcing to keep up with the technical complexities in business processes; but what if these international standards are hampered by various factors such as local laws, regulations, policy, security aspect or organisation culture within the banks (operating in the developing countries in particular), which are the subject of the study? Previous studies that were reviewed did not study this aspect of the commercial banking sector and did not link the extent of the IT capabilities to enable e-banking services or even research on banks operating in developing countries, which was the aim of this study.
There is a clear gap in the field of research studies pertaining to developing countries. There is lack of research on the banks in developing countries from the viewpoint of investors, technical solutions providers, or decision-makers within those banks.
Most of the banks strive to remain updated with the modern and advanced systems of banking operations. It is important to know the role of development of information and communications technology (ICT) to give banks the opportunity to provide innovative financial services so that they become most versatile and comfortable without adding new branches.
Methods
This research illustrated the methodology of designing a case study, collecting data, and analysing data. A framework was designed that contained internal variables that affected the capabilities of IT to enable e-banking services. The case study strategy was chosen to answer the research question regarding realistic service in the banking sector, especially in developing countries.
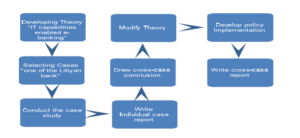
This strategy helped to discover how or why IT capabilities enabled e-banking. This approach helps to understand or diagnose the problem in a more comprehensive study, which helps open the area for further research. The case study was focused on the Gumhouria Bank, Libya. For applying the above concepts to the current draft of the study focusing on the Gumhouria bank, a step-by-step process was set up:
1.Assess the level of e-banking services in Libyan banks and in developing countries.
2.Determine the level of e-services in Libyan banks associated primarily with technical resources available and the investment in IT in Libya.
3.Discover the necessary level to provide the required e-services to bank customers to meet their needs.
4.Identify the IT capabilities and necessary components to provide e-banking services of high quality.
5.Framework that is considered to form the basis of IT capabilities that enables e-banking.
6.Identify the internal variables that have an impact on the relationship of IT capabilities and e-banking, focusing on those that can raise the level of e-banking services.
The time period for the case study was from 2005—2009. This period was vital in understanding the ISec variable and its impact on e-banking because of the rapid changes that occurred during that period in the Libyan banking sector and within the bank, in particular.
This change included the development of the bank infrastructure and establishment of a core banking system to take into account the international standards in the management of banking operations.
Previously, the bank dealt with its customers through different local systems; these systems were not able to provide integrated e-services to its customers. The main weakness was on the availability side. For example, the local systems were not linked with centralised databases.
This resulted in problems with follow-up and maintenance, complications in modernisation and development, middleware problem between the ATMs and the bank system, challenges in adopting merge technologies, frequent need to use banking operations manually, and provision of e-banking that did not exceed the borders of the branch building.
Therefore, the Gumhouria Bank tried to find new channels to provide e-banking services to its customers, with a focus on reducing the level of concern in regard to ISec. This study highlighted information security (ISec) as one of the variables that could affect the level of e-banking in Libyan banks.
This study adopted the flowchart model suggested by Yin (2003) (Figure 1).
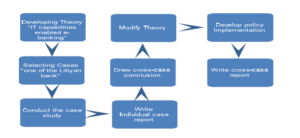
Figure 1: Case Study Method (Source: Yin, 2003, p. 50)
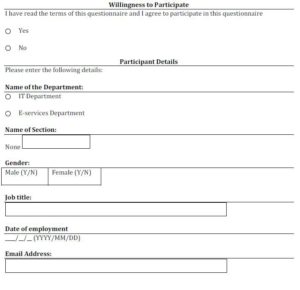
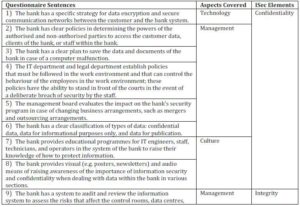
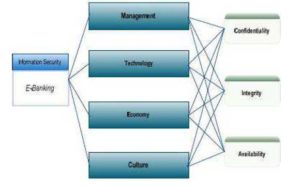
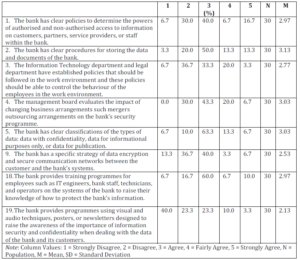
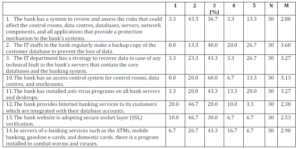
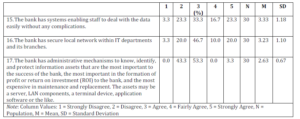
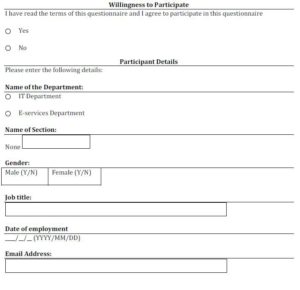
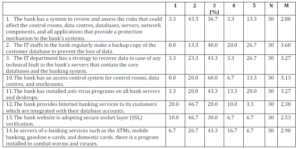
The study focused on a small IT-skilled work group in two technical departments in a commercial bank in Lybia: the IT department and the electronic services department. The question structure was in the Likert scaling format. The survey contained 19 sentences (Table 3).
Table 3: Questionnaire
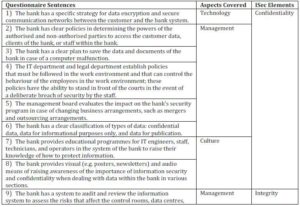
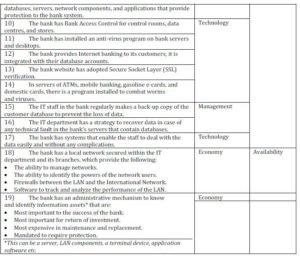
The researcher designed this questionnaire to cover these four aspects and explained the impact of ISec through the CIA elements. The participants had to evaluate the 19 sentences with one of these responses: strongly agree, fairly agree, agree, disagree, or strongly disagree. The participants’ responses would show the impact of a changing ISec on e-banking services.
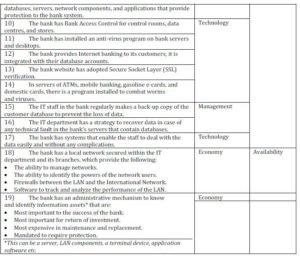
These 19 sentences were selected to interpret and illustrate the impact of ISec variables on e-banking services. According to Whitman and Mattrod (2010), these variables are linked to three main elements of CIA.
These three elements, according to Syamsuddin and Hwang (2009), can be studied through four aspects: management, technology, economy, and culture (Figure 2).
With regard to the online survey on how the ISec and CIA triangle was applied inside the bank correctly, the responses of 30 participants out of 50 employees working in the IT and e-services departments in the Gumhouria Bank were recorded.
The online survey contained a number of statements which the participants were required to evaluate by selecting their degree of satisfaction with these statements based on their work experience and knowledge (Appendix A). The participants were required to assess these statements technically from an information security perspective. The statements were mainly about Information Security (ISec) factors inside Gumhouria Bank, and classified into four areas: 1- Management, 2- Technology, 3- Economy, and 4- Culture. SPSS software (Version 18) was used to analyse the data in a descriptive statistics format and to conduct complex statistical analyses. ANOVA was used to determine whether there was a difference in mean scores for the three aspects of information security (CIA aspects).
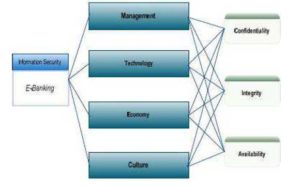
Figure 2: Information Security Structure, Syamsuddin and Hwang (2009)
Results
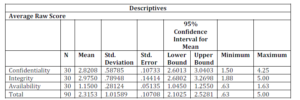
The results showed that the variable ISec (dependent variable) was one of the factors that affected the level of performance (independent variable), which was already assumed to link the capabilities of IT and e-banking services. The analytical part focused on ISec through three main aspects: confidentiality, integrity, and availability.
This analysis concluded that the element of integration is the most important element required by the banks followed by confidentiality and availability. The researcher can state that the availability score is statistically lower than that of confidentiality and integrity.
There is no statistical difference between confidentiality and integrity. As availability has a lower score compared to others and is statistically different, it stems from the survey that the participants have a negative perspective on the availability aspect of the concerned organisation.
The responses on the confidentiality section show the bank’s clear policies in determining who is authorised and not authorised to access the bank system, which was confirmed by 40% of the participants (Table 4). But the bank does not have a documented policy that describes or explains the work procedures, which must be followed inside the bank to access the bank system.
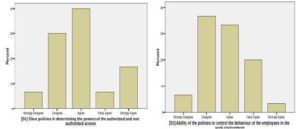
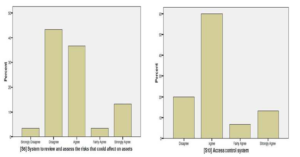
This was confirmed by 36% of participants. In sentence 1 and 3, there is a clear debate about this aspect from the IT and e-service departments (Figure 3).
Table 4: Summary Results for Confidentiality Element
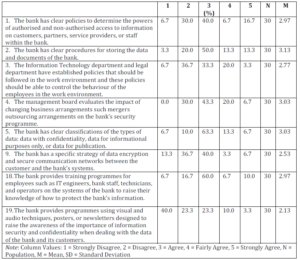
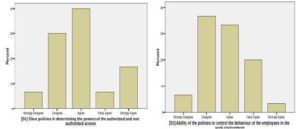
Figure 3: Bar Chart Shows the Reponses on Sentence 1 and 3
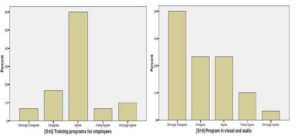
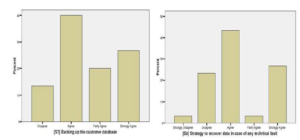
The bank offered a training programme to improve the level of knowledge about how the ISec factor is vital to the bank operations and e-banking. This was confirmed by 60% of participants (Figure 4[S18]). However, the results showed that the bank neglected the visual aids, which help to raise the security-awareness level among the employees of the bank and minimize the hazards in dealing with bank information (Figure 4[S19]).
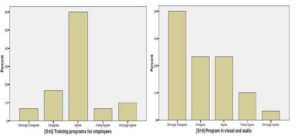
Figure 4: Bar Chart Shows the Reponses on Sentence 18 and 19
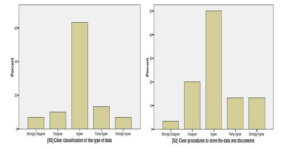
Enterprises and banks in particular are keen on data classification. This was confirmed by 60% of participants (Figure 5[S5]). The results showed that the bank set a strategy in classifying the data into confidential data, data for informational purposes only, and data for publication, which aimed to raise the level of confidentiality. Also, the bank had a clear procedure for storing data and documents (Figure 5[S2]).
Figure 5: Bar Chart Shows the Responses on Sentence 5 and 2
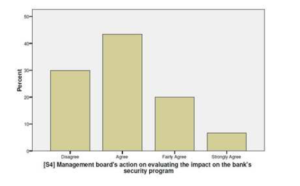
There were different views as to whether the bank had a specific strategy in evaluating the impact of outsourcing on security programme or not (Figure 6).
Figure 6: Bar Chart Shows the Responses on Evaluates the Impact of Outsourcing on Security Program
Table 5: Summary Results for Integrity Element
With regard to the integrity element (Table 5), the survey results in Figure 7(S10) shows that although the bank owns access control system for data centers and control rooms, the bank does not have a system to review and assess the risks that could affect the control rooms, data centers, databases, servers, network components, and all applications that provide a protection mechanism to the bank’s systems. Around 43% of participants confirmed this whereas 36.7% opposed it (Figure 7[S6]).
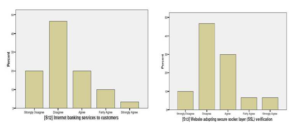
Table 5 and Figure 8 (S7 and S8) indicate that the bank used protection mechanism to secure the e-banking service and could recover the system any time. This was confirmed by 40% of participants. According to the IT staff response (Figure 9[S12 and S13]), the main challenge for the bank was how to offer a secure Internet banking package to the bank’s customers after deploying the core banking system. This part needs further research.
Figure 7: Bar Chart Shows the Reponses on Sentence 6 and 10
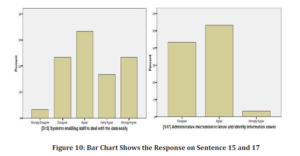
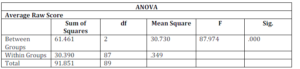
In the survey responses regarding availability, the results show that the bank system provides this feature and this is due to the bank adopting the i-FlexCube system as core banking (Table 6 and Figure 10[S15]).To determine whether there was a difference in mean scores for the three aspects of information security, an ANOVA was conducted (Table 7).
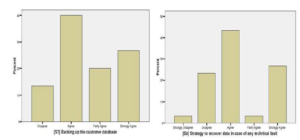
Figure 8: Bar Chart Shows the Response on Sentence 7 and 8
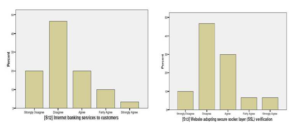
Figure 9: Bar Chart Shows the Response on Sentence 12 and 13
Table 6: Summary Results for Availability Element
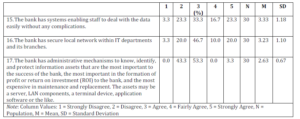
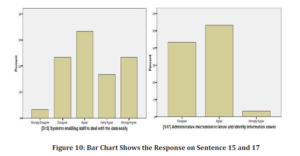
Table 7: Average Raw Score via ANOVA
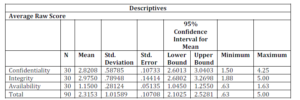
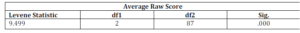
The Levene’s test was significant, F (2, 87) = 9.50, p < .05. Thus, the variances of the three aspects: confidentiality, integrity and availability are different to each other (Table 8).
Table 8: Test Homogeneity of Variances
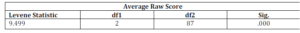
Table 9 shows that the ANOVA was significant, F (2, 87) = 87.97, p < .05.
Table 9: Averages Raw Score Between/Within Groups
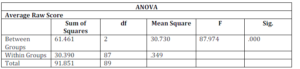
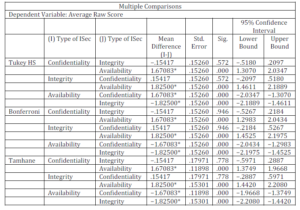
At least one aspect has a different mean score than the others (Table 10). To find out which mean score is different to what, post-hoc tests were conducted.
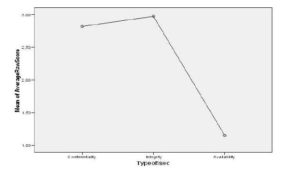
Since the group variances were not equal, using Tamhane’s post-hoc comparisons, it was revealed that the availability mean score was different from that of confidentiality and integrity. Mean scores of confidentiality and integrity were not statistically different to each other. A mean plot confirmed this conclusion (Figure 11).
Table 10: Dependent Variable by Multiple Comparisons
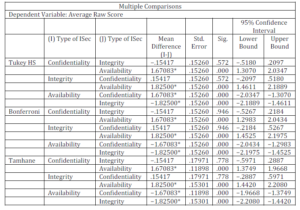
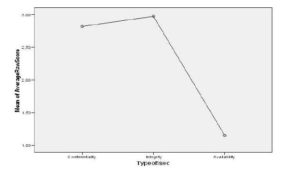
Figure 11: Mean Plot Confirmation
Conclusion
The present study compiled and examined a number of previous studies that focused mainly on IT capabilities and e-banking. The overall body of research inferred, but did not directly discuss IT capabilities in enabling e-banking. This paper tried to link the IT capabilities with e-banking.
The research found that IT capabilities are divided into three levels, and these levels can be described as components of IT capabilities, which helps to identify the variables or the elements that would directly affect the content of IT capabilities. The study also concluded that the outcome of IT capabilities can be seen as a performance from a technical perspective.
The author has interpreted this performance based on four dependant variables: security, reliability, data integrity, and regulatory environment. These four variables can also be considered from the perspective of e-banking as capabilities. The study helped to configure a model framework that contributes to create and determine the IT capabilities needed to operate an e-services model, particularly in developing countries.
This study’s framework showed the components of IT capabilities and e-banking. Many internal variables were proposed. This study identified ‘performance’ as an independent variable that linked IT capabilities and e-banking. The performance was interpreted by the researcher into four variables: security, reliability, data integrity, and the regularity environment.
However, due to time constraints, the researcher examined only one variable. Therefore, in order to clarify and understand the performance variable, there is a need to fully study the rest of the variables to find which of these three factors are vital for the performance variable and how these factors can be analysed and examined. Future research on these variables can explain and determine the key elements needed by the e- banking services in the banking sector, particularly in developing countries.
Acknowledgment
This effort was the result of research and study, which required significant amount of time. Here I will never forget the sacrifices of my wife, who stood by me, and gave me the necessary time to complete this project. I also express deep gratitude to my parents for their contribution in my education. This research also required, in some cases, academic advice and technical suggestions from some specialists in the field of information technology. I extend my sincere thanks to Professor Peter Hyland, who encouraged me and gave me the confidence in my abilities to write this scientific research.
References
Al-Hajri, S. (2008). “The Adoption of E-Banking: The Case of Omani Banks,” International Review of Business Research Papers, 4(5), 120-128.
Publisher – Google Scholar
Almazari, A. A. K. & Siam, A. Z. (2008). “E-Banking: An Empirical Study on the Jordanian Commercial Banks,” Journal of King Abdulaziz University, Economics and Administration, 22(2), 3-26.
Publisher – Google Scholar
Al Saud, A. F. & Abdallah, A. E. (2004). “A Framework for Analyzing & Comparing E-Banking Capabilities,” IADIS International Conference e-Society, 179-186.
Publisher – Google Scholar
Araya, S., Chaparro, J., Orero, A. & Joglar, H. (2007). “An Integrative View of IS/IT and Organizational Resources and Capabilities,” Issues in Informing Science and Information Technology, 4, 629-639.
Publisher – Google Scholar
Auta, E. M. (2010). “E-Banking in Developing Economy: Empirical Evidence from Nigeria,” Journal of Applied Quantitative Methods, 5(2), 212-222.
Publisher – Google Scholar
Ben-Jadeed, M. & Molina, A. (2004). “The Emergence and Evolution of e-Banking in Saudi Arabia: The Case of Samba Financial Group,” Frontiers of E-Business Research, 1, 90-106.
Publisher – Google Scholar
Berger, A. N. (2003). “The Economic Effects of Technological Progress: Evidence from the Banking Industry,” Journal of Money, Credit and Banking, 35(2), 141-176.
Publisher – Google Scholar
Bharadwaj, A. S. (2000). “A Resource-Based Perspective on Information Technology Capability and Firm Performance: An Empirical Investigation,” Mis Quarterly, 24(1), 169-196.
Publisher – Google Scholar
Bharadwaj, A. S., Bharadwaj, S. G. & Konsynski, B. R. (1999). “Information Technology Effects on Firm Performance as Measured by Tobin’s q,” Management Science, 45(7), 1008-1024.
Publisher – Google Scholar
Davenport, T. H. (2005). “The Coming Commoditization of Processes,” Harvard Business Review [Online], [Retrieved September 4, 2011], Available: http://www.birkenkrahe.com/teaching/ws07/materials/davenport_process_hbr_article
Publisher – Google Scholar
De Jong, A., Kolthof, A., Pieper, M., Tjassing, R., van der Veen, A. & Verheijen, T. (2009). ‘Itil® V3 Foundation Exam — The Study Guide,’ In van Bon, J. (ed), Van Haren Publishing, Zaltbommel, Scotland.
Floh, A. & Treiblmaier, H. (2006). “What Keeps the E-Banking Customer Loyal? A Multigroup Analysis of the Moderating Role of Consumer Characteristics on E-Loyalty in the Financial Service Industry,” Journal of Electronic Commerce Research, 7(2), 97-110.
Publisher – Google Scholar
Holland, C. P. & Westwood, J. B. (2001). “Product-Market and Technology Strategies in Banking,” Communications of the ACM, 44(5), 53-57.
Publisher – Google Scholar
Jiao, H., Chang, I. C. & Lu, Y. (2008). “The Relationship on Information Technology Capability and Performance: An Empirical Research in the Context of China’s Yangtze River Delta Region,” In: Industrial Engineering and Engineering Management. IEEM 2008. IEEE International Conference on Engineering Profession; Power, Energy, & Industry Applications, 872-876.
Publisher – Google Scholar
Lee, D. M. S., Trauth, E. M. & Farwell, D. (1995). “Critical Skills and Knowledge Requirements of IS Professionals: A Joint Academic/Industry Investigation,” Mis Quarterly, 19(3), 313-340.
Publisher – Google Scholar
Liao, Z. & Cheung, M. T. (2003). “Challenges to Internet E-banking,” Communications of the ACM, 46(12), 248-250.
Publisher – Google Scholar
Mithas, S., Ramasubbu, N., Krishnan, M. S. & Sambamurthy, V. (2004). “Information Technology Infrastructure Capability and Firm Performance: An Empirical Analysis,” [Online], Available: http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.113.9482&rep=rep1&type=pdf
Publisher
Mols, N. P. (1998). “The Behavioral Consequences of PC Banking,” International Journal of Bank Marketing, 16(5), 195-201.
Publisher – Google Scholar
Okunoye, A., Bada, A. O. & Frolick, M. (2007). “IT Innovations and e-service Delivery: An Exploratory Study,”Proceedings of the 9th International Conference on Social Implications of Computers in Developing Countries, São Paulo, Brazil, 1-8.
Publisher – Google Scholar
Rahman, I. U. (2007). “Role of Information Technology in Banking Industry,” Review of Business Research, 7(6).
Publisher
Saatcioglu, K., Stallaert, J. & Whinston, A. B. (2001). “Design of a Financial Portal,” Communications of the ACM, 44(5), 33-38.
Publisher – Google Scholar
Salehi, M. & Alipour, M. (2010). “E-Banking in Emerging Economy: Empirical Evidence of Iran,” International Journal of Economics and Finance, 2(1), 201-209.
Publisher – Google Scholar
Syamsuddin, I. & Hwang, J. (2009). “The Application of AHP Model to Guide Decision Makers: A Case Study of E-Banking Security,” Proceedings of the 2009 Fourth International Conference on Computer Sciences and Convergence Information Technology, IEEE Computer Society, 1469-1473.
Publisher – Google Scholar
Tshinu, S. M., Botha, G. & Herselman, M. (2008). “An Integrated ICT Management Framework for Commercial Banking Organisations in South Africa,” Interdisciplinary Journal of Information, Knowledge, and Management, 3, 39-53.
Publisher – Google Scholar
Wei, J. & Howell, J. (2010). ‘Value Increasing Model in Commercial E-Banking,’ Journal of Computer Information Systems, 51(1), 72-81.
Google Scholar
Whitman, M. E. & Mattord, H. J. (2010). Management of Information Security, Boston, USA, Course Technology Cengage Learning.
Publisher – Google Scholar
Wu, J.- H., Hsia, T.- L. & Heng, M. S. H. (2006). “Core Capabilities for Exploiting Electronic Banking,” Journal of Electronic Commerce Research, 7(2), 111-122.
Publisher – Google Scholar
Yin, R. K. (2003). Case Study Research Design and Methods, Sage Publications, New Delhi, India.
Publisher – Google Scholar
Yoon, C. Y. (2011). “Measuring Enterprise IT Capability: A Total IT Capability Perspective,” Knowledge-Based Systems, 24(1), 113-118.
Publisher – Google Scholar
Yoon, C. Y., Bae, Y. J., Chung, S. S., You, J. C. & Hong, S. K. (2010). “Measuring Individual IT Capability to Efficiently Perform Business Tasks in an Enterprise IT Environment,” In: Industrial Engineering and Engineering Management (IEEM), IEEE International Conference, 168-172.
Publisher – Google Scholar
Appendix A
The following Questionnaire was used for the online survey.